What is MFA?
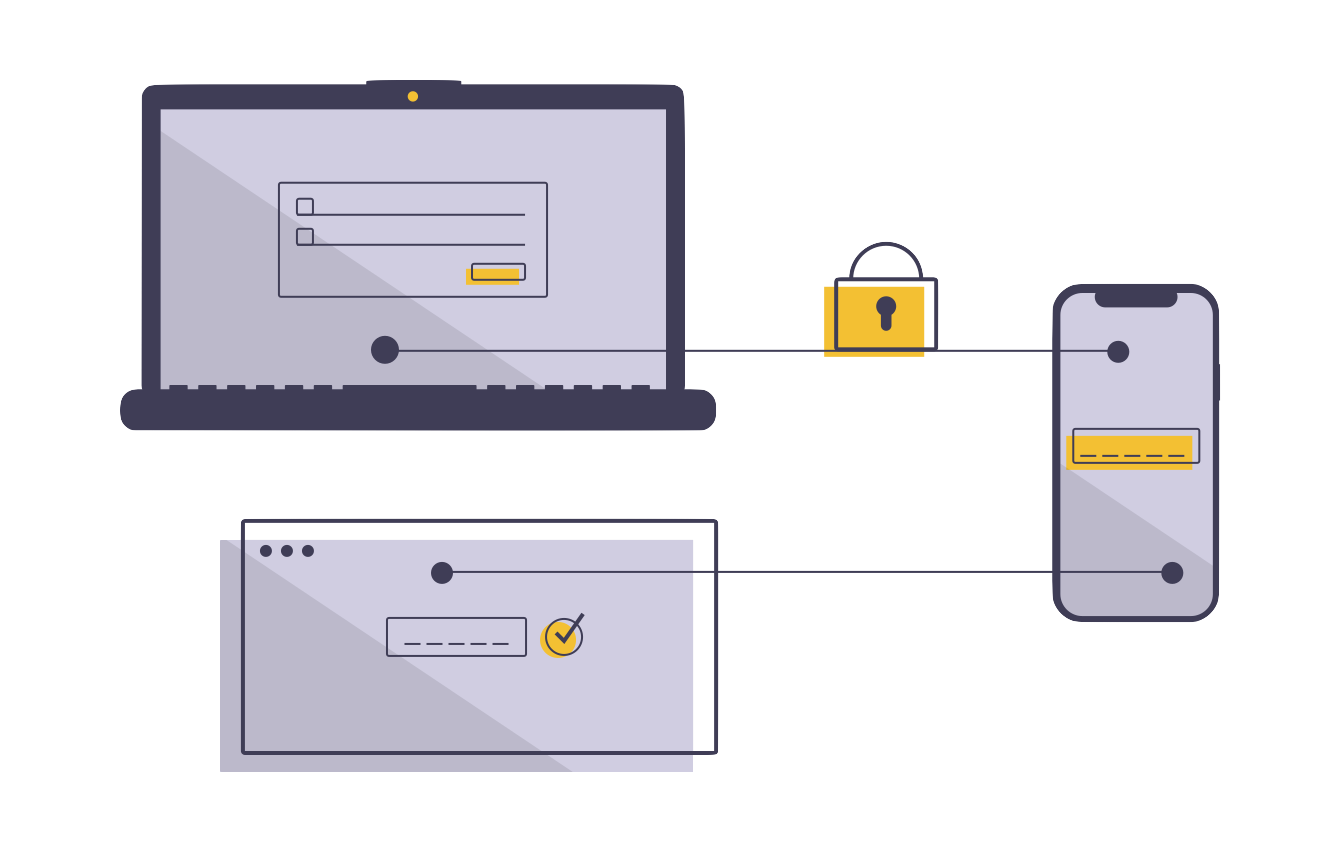
Multi-factor authentication (also called 2-factor authentication or 2-step verification) adds security layers to your traditional username and password in order to protect your accounts and devices from unauthorized access. With MFA enforced, authentication is allowed only when a verification method other than your password — usually a one-time password or login confirmation from a device in your possession — validates your identity.
As work-from-anywhere becomes the norm, access to confidential information is no longer protected by physical access to an office or to a desktop computer. With traditional credentials, someone could log into your company’s Dropbox account from anywhere in the world if your password has been compromised. MFA is one of the most effective and easiest layers to add for preventing this kind of unauthorized access and improving your digital security. You really should be using MFA everywhere it’s available.
You probably already use MFA
You may already use MFA on some of your accounts. For example:
- When logging into your bank’s online portal with your username and password, a 6-digit code is sent to your mobile number.
- Your company uses Microsoft 365 for email, and when you sign in to your account you get a push notification from the Microsoft Authenticator app on your mobile phone.
- Your company allows you to work from home but, when you do, you need to keep a USB dongle attached to your computer in order to access your company email account.
- You get a new MacBook, and when signing in to your Apple ID with your username and password you get a push notification or authentication code on another Apple device you own (e.g. your iPhone or iPad) that is already signed in to the same Apple ID.
Something you know + something you have
In all four cases, your username and password together are not enough to gain access. You also need something that you have physical access to — your mobile phone, a USB dongle, another Apple device — to gain access. That’s why MFA is often described as something you know (e.g. your password) plus something you have (e.g. your phone). Requiring both makes it much more likely that the person accessing your account is really you.
Verification codes and push notifications are time-sensitive. That 6-digit code your bank sent you is probably valid for no more than five minutes. The 6-digit codes you retrieve on an authenticator app will be valid for only 30 seconds. Push notifications are valid for only 60 seconds. Time limits for these additional authentication factors reduce the chances that someone can intercept them with enough time to impersonate you.
Biometric authentication (fingerprint or facial recognition), can also be used as an additional authentication method. In some cases, administrators can set up trust rules for specific devices, IP addresses, or geographic regions to reduce the number of devices that could potentially gain access to confidential information.
Centralized MFA
It can be a hassle to manage MFA for the many accounts you need to access. Each one might use a different method on a different device with a different time frame, which gets confusing. Worse, even if you carefully set up MFA for some accounts, you might forget another, opening a vulnerability in your systems.
Identity and access management (IAM) solutions are meant to tackle this challenge by rolling authentication for many different services into a single platform. With IAM properly configured and maintained, you’ll use a single sign-on (SSO) portal that has strong security requirements including enforced MFA, and from that portal be able to access the other systems you need.
Macktez Identity Management
To protect our clients’ systems with a centralized IAM solution, our Identity Management subscription manages verification for online services and local computer accounts so that users have a unified identity for authentication. MFA is always enforced for this service, and additional conditions can be added for clients with greater security needs and/or lower tolerance for risk. And with Identity Management, tightening security for one service automatically means tightening it for everything, maintaining a consistent security profile for your entire organization.